A leading IT and communications provider that has a complete communications and technology portfolio, was affected by an Emotet malware attack.
What is Emotet malware?
Emotet is a malware strain believed to be based in Ukraine. The malware, also known as Heodo, was identified for the first time in 2014 and was later determined to be one of the most common dangers of the decade.
Although the business had basic security, some unidentified vulnerabilities left it susceptible to a cyberattack. The malware was quickly contained and removed from the environment. Having a business continuity management framework helped the organization to do this.
The company could garner the following benefits through business continuity management:
• Increased internal efficiency.
• Minimized potential impact of business disruption.
• Improved customer satisfaction, with targets exceeded.
Let’s understand what business continuity management is.
Business continuity management (BCM) is the method of proactively planning and preparing an organization to continue operating normally or quickly resuming operations following a crisis. Determining potential dangers like fire, flood, or cyberattacks is another step in the process.
Business executives can plan to recognize and handle potential crisis before they occur. Following that, test the procedures to confirm that they are effective, and periodically evaluate the method to ensure that it is still relevant.
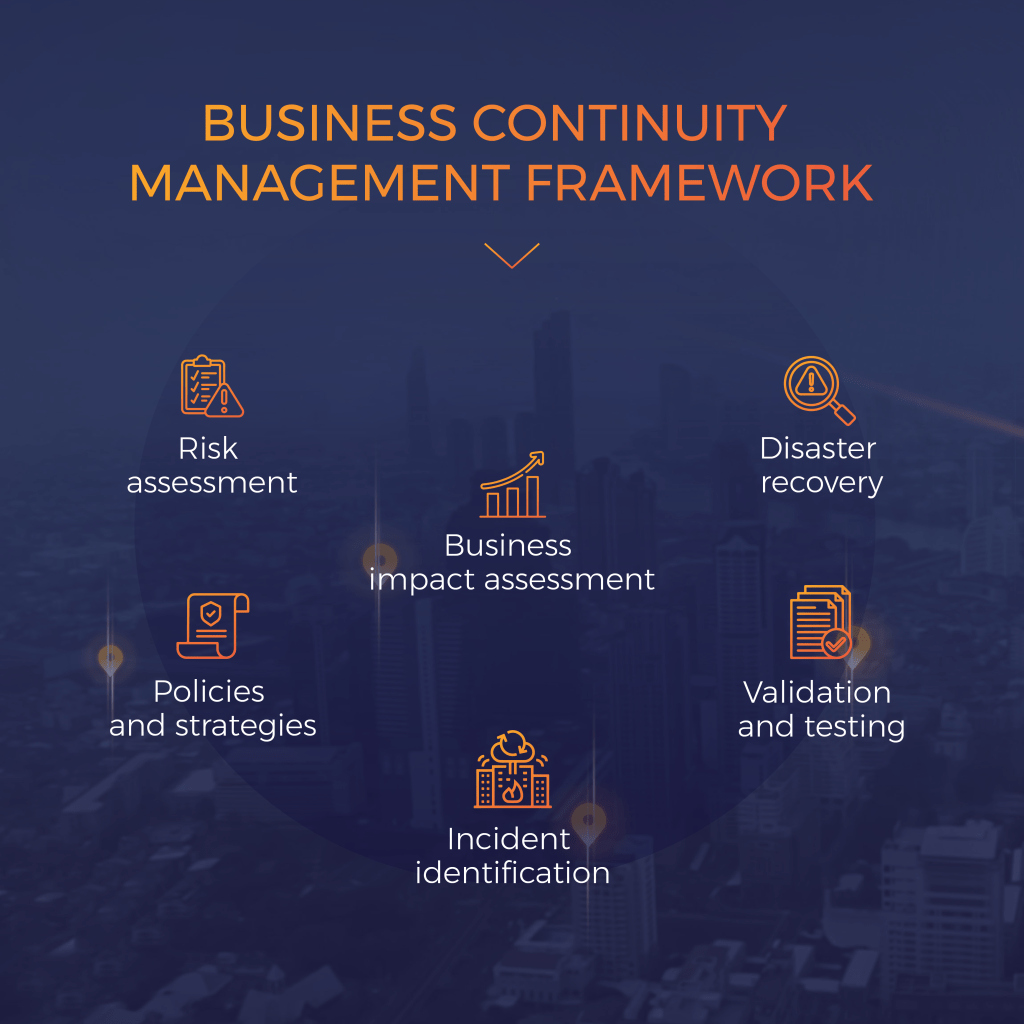
Business Continuity Management Framework
It describes the planning process for creating plans and protocols in advance to enable companies to react to an incident in a way that allows crucial business functions to continue within the predicted disruption levels.
Policies and Strategies: It starts with the policies and procedures created, examined, and used when an incident occurs. The program’s scope, main participants, and management structure are all described in the policy.
Businesses need to be clear about what is covered by a plan. During this phase, roles and responsibilities must also be assigned. The scope is equally important. It outlines the organization’s definition of business continuity.
Business Impact Assessment: The impact assessment is a cataloging procedure to determine your firm’s data and how and where it is stored. It establishes which data are the most important and how much downtime is tolerable if those data or apps are unavailable.
Although businesses strive for 100% uptime, with redundant systems and storage capacity, this rate is not always feasible. Calculating your recovery time objective, which is the maximum amount of time it would take to return applications to a functional condition in the event of an unexpected interruption of service, is another step you need to do during this phase.
Risk Assessment: Risk assessment identifies the wide range of hazards that might impact the business. The initial, and sometimes extensive, phase is to identify potential dangers. This comprises:
- Financial turbulence.
- Effects of manpower loss.
- Changing preferences of customers.
- Ability to respond to security problems with a plan.
Each risk needs to be defined and described in detail. The company must assess each risk’s likelihood of arising and its potential effects in the following phase.
Validation and Testing: Continuous monitoring, measurement, and testing of the hazards and their effects are required. After implementation, mitigation plans should be evaluated to ensure they are effective and coordinated.
Identification of Incidents: Determining what incident constitutes an incident is critical in business continuity management. Policy papers should define who or what can trigger an incident. These “trigger” events ought to activate the team and prompt the deployment of the established business continuity strategy.
Disaster Recovery: Disaster recovery is the process that takes place after an incident has occurred. It is the end consequence of the efforts to recognise and address risks. Disaster recovery focuses more on targeted incident reactions than comprehensive planning. One essential step following an incident is to debrief, evaluate the response, and adjust plans as necessary.
The lack of a business continuity plan entails serious dangers. Without a proper plan, the business would be ill-equipped to handle urgent difficulties. It can lead to downtime for servers, systems, and applications hosted in the cloud. Significant revenue can be lost even during brief downtimes. Another impact is the loss of credibility for a brand’s reputation and identity. Widespread, ongoing, or frequent downtime can damage consumers’ and customers’ trust.
CONCLUSION
Data protection and integrity management are essential for businesses because they can prevent catastrophic data loss. The culture of the company ought to include it. Businesses can speed up the recovery of crucial operations by using a systematic approach to business continuity planning. Know how Skillmine can help you plan your response to incidents better through a comprehensive business continuity management framework. Know more:
Looking for expert technology consulting services? Contact us today.


