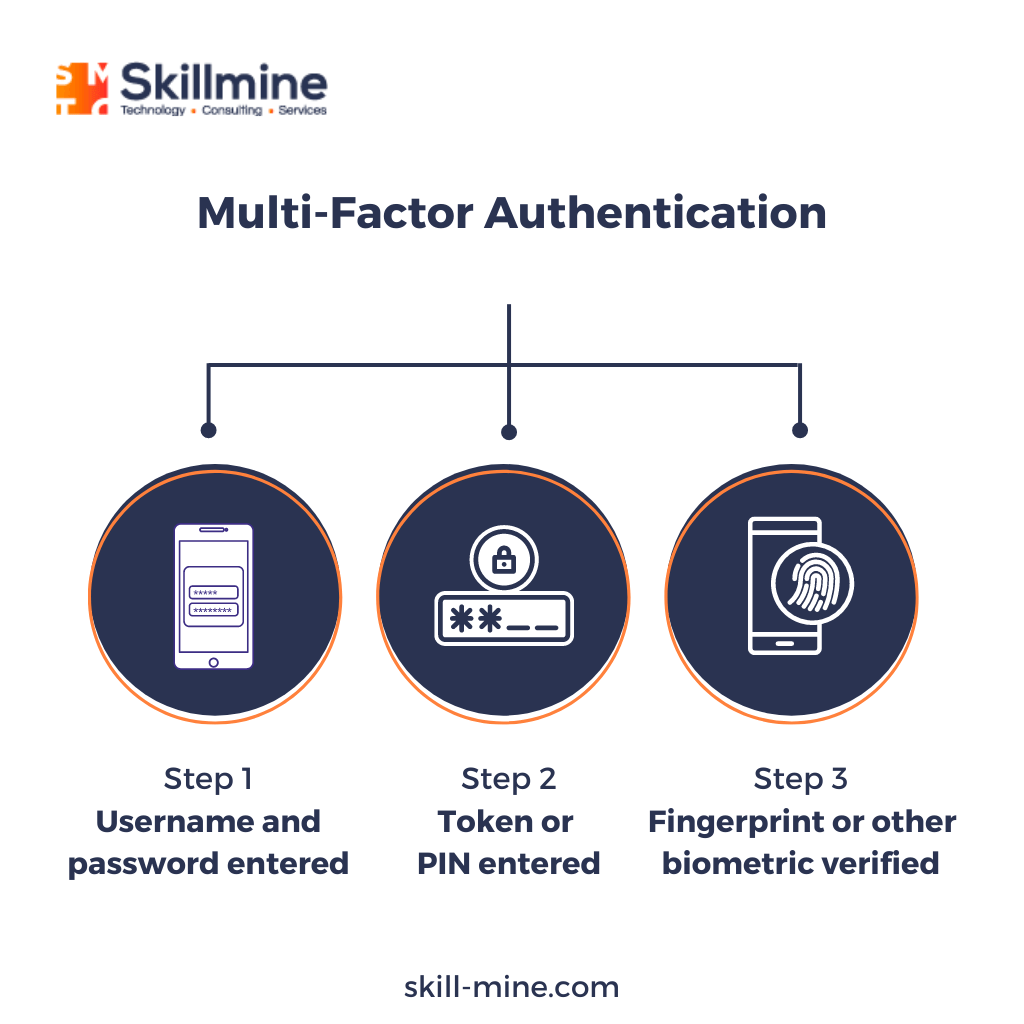
Multi-Factor Authentication (MFA) and access control have pivotal roles in safeguarding online accounts and sensitive data. However, staying abreast of the ever-evolving trends and groundbreaking innovations within these domains can be a daunting task. We shed light on the upcoming technologies and methodologies that are redefining the landscapes of MFA and access control.
Trends in MFA
Risk-based authentication
Vendors are integrating advanced authentication measures, like step-up or risk-based authentication. This strategic approach involves deploying more than just a second factor in specific scenarios. The underlying principle is to create a multi-tiered security process, requiring users to overcome increasingly stringent security measures when accessing more sensitive account activities.
This shift towards heightened security stems from the persistent threat posed by phishing attacks. Recognizing the need for stronger safeguards, vendors are crafting strategies that demand more rigorous authentication steps under certain circumstances. This strategy acts as a barrier against unauthorized access, safeguarding sensitive transactions and critical actions.
Despite the promising potential of risk-based authentication, it’s important to acknowledge that this approach is still in the process of refinement. Particularly within the realm of Single Sign-On (SSO) vendors, risk-based authentication is in its early stages.
In essence, risk-based authentication represents an evolutionary leap in security practices. By incorporating dynamic and adaptable authentication measures, organizations aim to mitigate the vulnerabilities exposed by phishing attacks. As the landscape continues to evolve, we can anticipate that risk-based authentication will mature, becoming an integral facet of security solutions, even though its present adoption comes at a notable cost.
The continuous evolution of biometrics
The realm of biometric security is witnessing significant evolution, propelled by innovative trends that are reshaping how we authenticate access to our applications and services. One notable trend is the integration of built-in fingerprint and facial readers, which have become standard features in contemporary Android and iOS smartphones.
Moreover, blockchain-based strategies are shining a light on more secure and breach-resistant biometric data distribution. Similarly, governments across the globe are leveraging blockchain to authenticate property transactions within their land registries.
However, despite these positive trends, a hurdle remains in the form of disparate API collections and code streams between Apple and Android platforms. While biometric capabilities are increasingly prevalent in modern smartphones, the same cannot be said for desktops and laptops. These devices, equipped with biometric sensors, are yet to be universally adopted.
Growth of smartphone authentication apps
Just three years ago, the innovative wave centred around leveraging smartphones for authentication through soft tokens. These tokens could take the form of a smartphone app, SMS messages, or even telephony. The popularity of smartphone apps has endured due to their swiftness and unmatched security, making them the most reliable method for deploying Multi-Factor Authentication (MFA) across an infrastructure.
Prominent players have all contributed to the growth of smartphone apps. Skillmine’s Authenticator is one such authentication and authorization app that combines MFA and single sign-on (SSO).
Authenticator’s widespread appeal can be attributed to its multi-platform compatibility, spanning tablets, laptops, and phones—a feature that remains a rarity among many MFA tools, which typically support either laptops or phones, but not both.
Conclusion
Every authentication approach remains vulnerable to attacks. However, organizations that possess an acute awareness of these vulnerabilities stand poised to craft educational initiatives and defensive strategies aimed at mitigating potential attack vectors. A meticulously devised multi-factor authentication framework, synergized with well-informed users, possesses the capacity to neutralize the majority of threats faced by businesses.
Looking for expert technology consulting services? Contact us today.


