As enterprises accelerate digital transformation, adopt hybrid work models and integrate AI-driven systems, the security and governance of endpoints directly influence business continuity, compliance posture and brand reputation. Every laptop, mobile device, server and virtual endpoint now represents both productivity potential and cyber risk exposure.
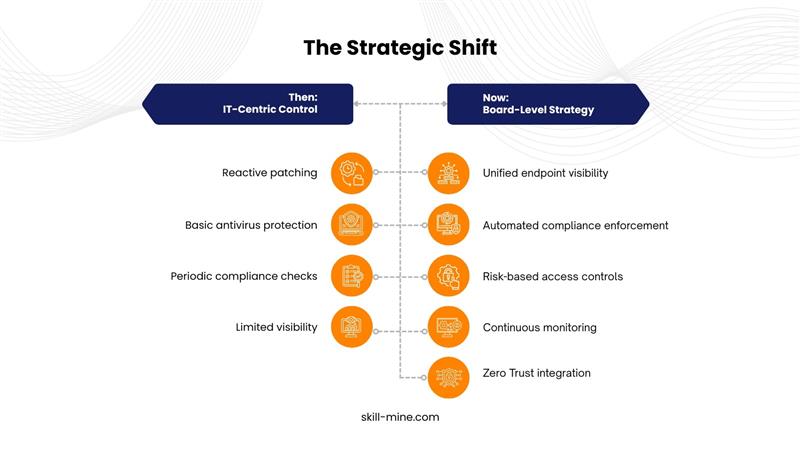
Forward-looking organizations are recognizing that modern Endpoint Management Platforms are not operational tools. They are strategic infrastructure investments.
Unlike traditional AI models that require frequent manual tuning, autonomous systems operate as closed-loop systems: observe → decide → act → learn.
- Hybrid and remote work environments
- Multi-cloud infrastructure SaaS-heavy application ecosystems
- Third-party contractor networks
- AI and data-driven operational systems
Modern enterprise endpoint management solutions provide:
- Real-time device visibility
- Automated patch management
- Endpoint compliance monitoring
- Configuration enforcement
- Integration with Zero Trust architecture
1. Cybersecurity Risk Is Enterprise Risk
Cyber incidents now impact stock value, customer trust and regulatory standing. Endpoint compromise is one of the most common breach entry points.
A centralized endpoint management strategy enables:
- Continuous monitoring of endpoint health
- Automated threat containment
- Enforcement of least privilege policies
- Integration with identity and access management systems
This alignment between endpoint posture and enterprise security strategy makes it a board-level concern.
2. Regulatory Compliance Requires Continuous Endpoint Control
Regulations such as SOC 2, ISO 27001 and regional data protection frameworks require strict control over endpoint security, logging and access governance.
Manual compliance tracking cannot scale across thousands of distributed devices.
Cloud-based endpoint management platforms support:
- Real-time compliance dashboards
- Audit-ready reporting
- Automated remediation workflows
- Policy enforcement across geographies
For leadership, this reduces audit friction and minimizes regulatory exposure.
3. Hybrid Work Demands Unified Device Visibility
In 2026, workforce flexibility is permanent. Employees access corporate systems from home networks, public Wi-Fi and international locations.
Without unified endpoint visibility, organizations face blind spots.
Unified Endpoint Management solutions provide:
- Centralized device inventory
- Remote configuration management
- Secure onboarding and offboarding
- Device posture validation before granting access
This ensures that productivity does not compromise governance.
4. AI Adoption Increases Endpoint Sensitivity
AI workloads rely on high-value data. Compromised endpoints can manipulate inputs, leak intellectual property or disrupt automated systems.
Board-level AI initiatives must include endpoint integrity as a foundational layer.
Endpoint management integrated with Zero Trust security ensures:
- Device compliance verification before access
- Adaptive access controls based on risk posture
- Continuous monitoring of device behavior
Secure AI transformation depends on endpoint governance.
Modern cybersecurity architecture is no longer siloed. Endpoint management now intersects with:
- Identity and Access Management
- Zero Trust Network Access
- Privileged Access Controls
- Data Loss Prevention systems
When endpoint posture signals integrate with identity systems, organizations can enforce adaptive security. A non-compliant device can automatically trigger restricted access or additional verification.
This convergence elevates endpoint management from an operational tool to a strategic control layer.
To treat endpoint management as a strategic investment, decision-makers should assess:
- Scalability across global operations
- Cloud-native architecture
- AI-driven threat detection capabilities
- Automated patch and vulnerability management
- Integration with existing security stack
- Real-time compliance and reporting features
Investments must support long-term governance, not just short-term cost optimization.
Skillmine’s Approach to Enterprise Endpoint Management
At Skillmine, we design and implement modern Endpoint Management Platforms aligned with enterprise security architecture and business objectives.
Our approach focuses on:
- Zero Trust aligned endpoint governance
- Automated policy enforcement
- Integration with identity and access systems
- Scalable cloud-native deployment
- Real-time compliance monitoring
We help organizations transform endpoint management from a reactive IT process into a strategic business safeguard.
In 2026, endpoint management directly impacts cyber resilience, regulatory readiness and operational efficiency. Boards can no longer delegate it solely to IT teams.
Organizations that invest in intelligent, integrated endpoint management platforms will strengthen their security posture, reduce compliance risk and enable confident digital growth.
Endpoint management is no longer a technical checkbox. It is a business imperative.





