A security operations centre (SOC) is a facility that contains an information security team that is in charge of continuously monitoring and assessing an organization’s security posture. The purpose of the SOC team is to use a combination of technical solutions and a robust set of procedures to identify, evaluate, and respond to cybersecurity problems.
Security analysts, engineers, and managers who supervise security operations play important roles in security operations centres. Staff from the SOC collaborate closely with organisational incident response teams to ensure that security vulnerabilities are handled as soon as they are discovered.
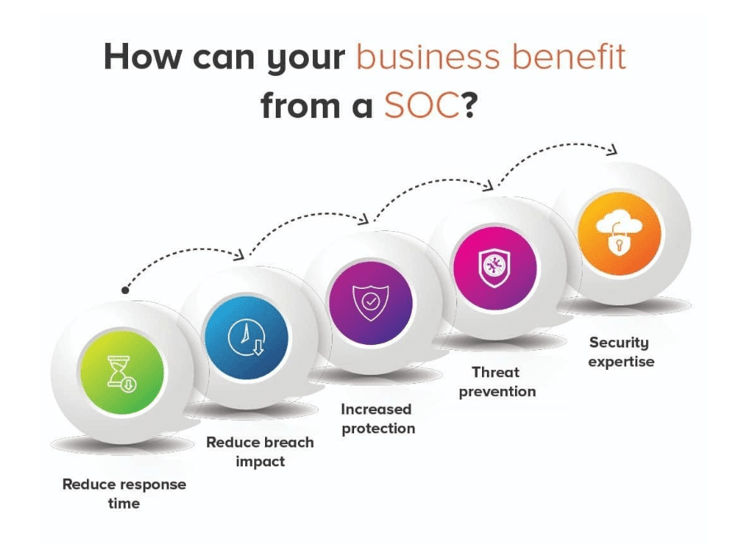
The enhancement of security incident detection through constant monitoring and analysis of data activity is a fundamental benefit of having a security operations centre. SOC teams are crucial for ensuring rapid detection and response to security issues by evaluating activity across an organization’s networks, endpoints, servers, and databases around the clock. A SOC’s 24/7 monitoring offers businesses an edge in defending against events and intrusions, regardless of source, time of day, or kind of assault.
In Verizon’s annual Data Breach Investigations Report, the gap between attackers’ time to compromise and businesses’ time to discovery is well documented. A SOC helps organisations bridge that gap and keep on top of the dangers facing their environments.
How does a SOC work?
The SOC team is responsible for the continuous, operational component of business information security. Rather than defining security strategy, building security architecture, or implementing protective measures, security analysts work together in the Security Operations Centre to identify, evaluate, respond to, report on, and prevent cybersecurity problems. To examine incidents, some SOCs have extensive forensic analysis, cryptanalysis, and malware reverse engineering capabilities.
The first stage in building an organization’s SOC is to explicitly identify a strategy that takes into account business-specific goals from multiple divisions, as well as to take input and support from the management. After the plan has been defined, the infrastructure that will support it must be put in place.
Firewalls, intrusion prevention systems (IPS/IDS), breach detection solutions, probes, and a security information and event management (SIEM) system are all part of a typical SOC infrastructure. In order to secure sensitive data and comply with industry or government standards, the SOC also monitors networks and endpoints for vulnerabilities.
Security automation is used by truly successful SOCs to become more effective and efficient. Organizations may boost their analytics capacity and better fight against data breaches and cyber threats by combining highly competent security analysts with security automation.
Looking for expert technology consulting services? Contact us today.

